The Basic Principles Of Risk Management Enterprise
Table of ContentsIndicators on Risk Management Enterprise You Need To Know8 Simple Techniques For Risk Management EnterpriseExcitement About Risk Management Enterprise
Control that can view or modify these aspects by establishing certain accessibility rights for individual users, making certain info security and tailored use. Enables individuals to tailor their user interface by selecting and arranging necessary data components. Offers a tailored experience by allowing personalization of where and just how data elements are shown.It permits access to real-time incorporated information quickly. Facilities can utilize detailed data intelligence for quicker and more informed decision-making.

Diligent is a risk monitoring software application that enables maximizing efficiency, and improves growth. It additionally assists monitor risks with ERM software that includes incorporated analytics and adapts to your business demands. This software application includes various useful attributes. Below we have actually highlighted one of the most important ones. So, examine them out.
About Risk Management Enterprise
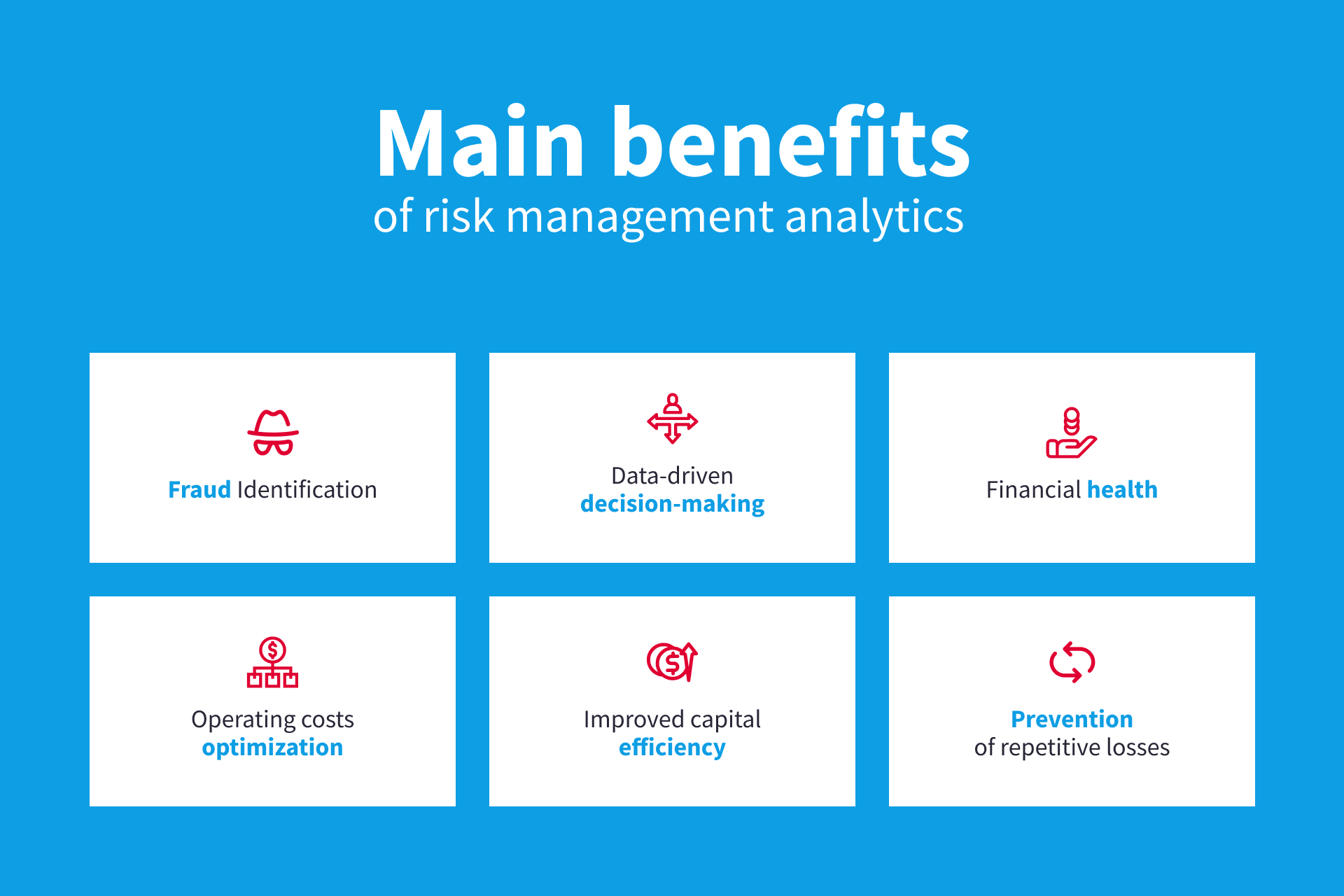
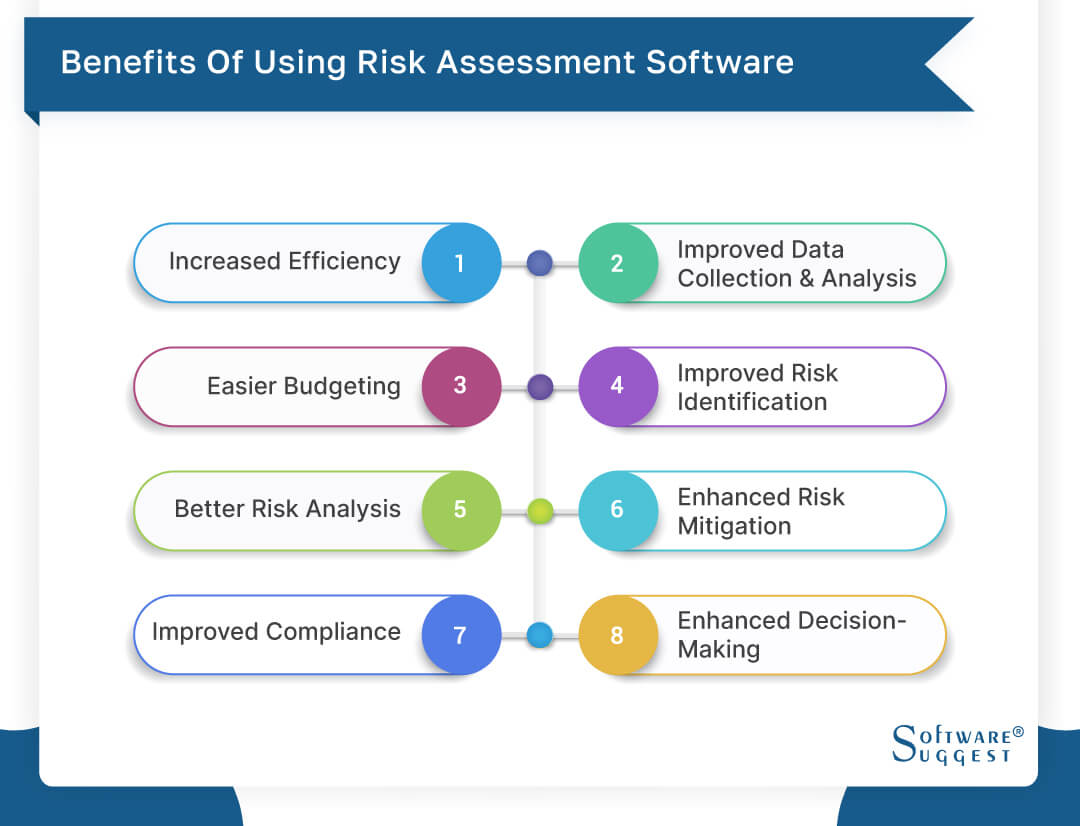
Streamlines the process of gathering threat data from various components of the company. Offers management and the board with real-time threat insights. Usage ACL's advanced analytics to spot risk patterns and predict dangers.
This permits business to capture threat understandings and red flags in the third-party vendor's safety and security report. Makes it possible for business to catch find more information and record threat understandings and red flags in third-party supplier safety and security records.
It also lowers danger via streamlined compliance and danger management. It can aid accumulate and track all your threats in the Hyperproof risk register.
It supplies quick accessibility to necessary details and paperwork. This view publisher site ensures the protection of Active evidence instances by enabling multi-factor verification (MFA) making use of authenticator applications such as Google Authenticator, Microsoft Authenticator, or Authy.
The 9-Minute Rule for Risk Management Enterprise
It enables smooth operations and combinations and minimizes inadequacies. It offers top-tier safety and security functions to safeguard delicate data. This threat administration software is an excellent tool for facilities wanting to repair unnecessary concerns or threats. It includes multiple types of features that make it certain for ERM managers. Here we have actually highlighted some of its vital functions for your advantage, so have a look.
Users can additionally make use of the AI-powered devices and pre-existing content to create, evaluate, focus on, and address dangers successfully. Streamlines the procedure of configuring and inhabiting danger signs up. Uses see AI and library web content to improve threat assessment precision. It makes it possible for much faster identification and mitigation of threats, This is mainly an aesthetic design.
Comments on “The Risk Management Enterprise Statements”